應用程序簽名允許開發人員識別應用程序的作者並更新他們的應用程序,而無需創建複雜的接口和權限。在 Android 平台上運行的每個應用程序都必須由開發人員簽名。嘗試在未簽名的情況下安裝的應用程序將被 Google Play 或 Android 設備上的軟件包安裝程序拒絕。
在 Google Play 上,應用程序簽名連接了 Google 對開發人員的信任以及開發人員對其應用程序的信任。開發人員知道他們的應用程序未經修改就提供給了 Android 設備;開發人員可以對其應用程序的行為負責。
在 Android 上,應用程序簽名是將應用程序放入其應用程序沙箱的第一步。簽名的應用程序證書定義了哪個用戶 ID 與哪個應用程序相關聯;不同的應用程序在不同的用戶 ID 下運行。應用程序簽名確保一個應用程序不能訪問任何其他應用程序,除非通過明確定義的 IPC。
當應用程序(APK 文件)安裝到 Android 設備上時,包管理器會驗證 APK 是否已使用該 APK 中包含的證書正確簽名。如果證書(或更準確地說,證書中的公鑰)與用於簽署設備上任何其他 APK 的密鑰匹配,則新 APK 可以選擇在清單中指定它將與另一個類似地共享 UID - 簽名的 APK。
應用程序可以由第三方(OEM、運營商、替代市場)簽名或自簽名。 Android 使用自簽名證書提供代碼簽名,開發人員無需外部協助或許可即可生成這些證書。申請不必由中央機構簽署。 Android 目前不對應用證書進行 CA 驗證。
應用程序還能夠在簽名保護級別聲明安全權限,將訪問權限限制為僅使用相同密鑰簽名的應用程序,同時保持不同的 UID 和應用程序沙箱。通過共享 UID 功能允許與共享應用程序沙箱建立更密切的關係,其中使用相同開發人員密鑰簽名的兩個或多個應用程序可以在其清單中聲明共享 UID。
APK 簽名方案
Android 支持三種應用簽名方案:
- v1 方案:基於 JAR 簽名
- v2 方案: APK 簽名方案 v2 ,在 Android 7.0 中引入。
- v3 方案: APK 簽名方案 v3 ,在 Android 9 中引入。
為了獲得最大的兼容性,請使用所有方案對應用程序進行簽名,首先使用 v1,然後使用 v2,然後使用 v3。 Android 7.0+ 和更新的設備安裝使用 v2+ 方案簽名的應用程序比僅使用 v1 方案簽名的應用程序更快。較舊的 Android 平台忽略 v2+ 簽名,因此需要應用程序包含 v1 簽名。
JAR 簽名(v1 方案)
APK 簽名從一開始就是 Android 的一部分。它基於簽名的 JAR 。有關使用此方案的詳細信息,請參閱有關簽署您的應用程序的 Android Studio 文檔。
v1 簽名不保護 APK 的某些部分,例如 ZIP 元數據。 APK 驗證者需要處理大量不受信任(尚未驗證)的數據結構,然後丟棄未包含在簽名中的數據。這提供了相當大的攻擊面。此外,APK 驗證程序必須解壓縮所有壓縮條目,消耗更多時間和內存。為了解決這些問題,Android 7.0 引入了 APK 簽名方案 v2。
APK 簽名方案 v2 & v3(v2+ 方案)
運行 Android 7.0 及更高版本的設備支持 APK 簽名方案 v2(v2 方案)及更高版本。 (在 Android 9 中,v2 方案已更新為 v3,以在簽名塊中包含其他信息,但其他工作方式相同。) APK 的內容經過哈希處理和簽名,然後將生成的 APK 簽名塊插入 APK。有關將 v2+ 方案應用於應用程序的詳細信息,請參閱APK 簽名方案 v2 。
在驗證期間,v2+ 方案將 APK 文件視為一個 blob,並對整個文件執行簽名檢查。對 APK 的任何修改(包括 ZIP 元數據修改)都會使 APK 簽名無效。這種形式的 APK 驗證速度要快得多,並且可以檢測更多類別的未經授權的修改。
新格式是向後兼容的,因此使用新簽名格式簽名的 APK 可以安裝在較舊的 Android 設備上(它們只是忽略添加到 APK 中的額外數據),只要這些 APK 也是 v1 簽名的。
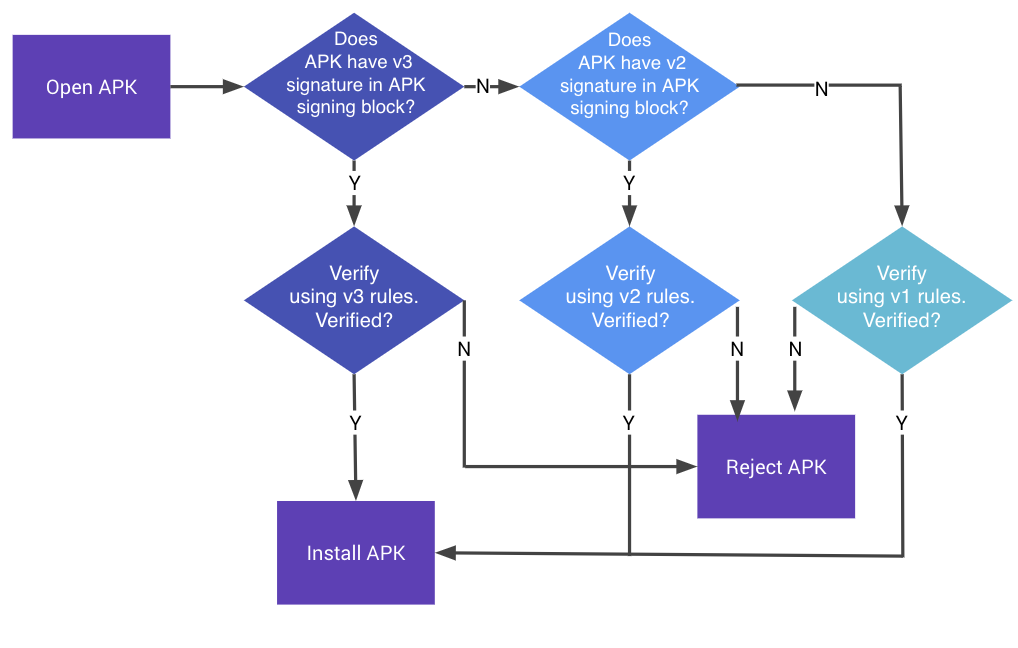
圖 1. APK 簽名驗證流程
APK 的整個文件哈希根據存儲在 APK 簽名塊中的 v2+ 簽名進行驗證。哈希涵蓋了除包含 v2+ 簽名的 APK 簽名塊之外的所有內容。在 APK 簽名塊之外對 APK 進行的任何修改都會使 APK 的 v2+ 簽名無效。帶有剝離 v2+ 簽名的 APK 也會被拒絕,因為它們的 v1 簽名指定 APK 是 v2 簽名的,這使得 Android 7.0 和更新版本拒絕使用它們的 v1 簽名驗證 APK。
APK簽名驗證流程詳見APK簽名方案v2的驗證部分。

