В этой статье рассказывается, как строится политика SELinux. Политика SELinux построена на основе комбинации основной политики AOSP (платформа) и политики конкретного устройства (поставщик). Поток сборки политики SELinux для Android 4.4–7.0 объединил все фрагменты sepolicy, а затем создал монолитные файлы в корневом каталоге. Это означало, что поставщики SoC и производители ODM boot.img (для устройств, отличных от A/B) или system.img (для устройств A/B) каждый раз, когда изменялась политика.
В Android 8.0 и более поздних версиях политика платформы и поставщика создается отдельно. SOC и OEM-производители могут обновлять свои части политики, создавать свои образы (например, vendor.img и boot.img ), а затем обновлять эти образы независимо от обновлений платформы.
Однако, поскольку модульные файлы политик SELinux хранятся в разделах /vendor , процесс init должен монтировать системный раздел и разделы производителя раньше, чтобы он мог читать файлы SELinux из этих разделов и объединять их с основными файлами SELinux в системном каталоге (перед загрузкой их в ядро).
Исходные файлы
Логика сборки SELinux находится в этих файлах:
-
external/selinux: внешний проект SELinux, используемый для создания утилит командной строки HOST для компиляции политики и меток SELinux.-
external/selinux/libselinux: Android использует только подмножество внешнего проектаlibselinuxвместе с некоторыми специфическими для Android настройками. Подробнее см.external/selinux/README.android. -
external/selinux/libsepol: -
external/selinux/checkpolicy: компилятор политик SELinux (исполняемые файлы хоста:checkpolicy,checkmoduleиdispol). Зависит отlibsepol.
-
-
system/sepolicy: базовые конфигурации политик Android SELinux, включая контексты и файлы политик. Основная логика сборки sepolicy также находится здесь (system/sepolicy/Android.mk).
Подробнее о файлах в system/sepolicy Реализация SELinux .
Android 7.0 и более ранние версии
В этом разделе рассказывается, как создается политика SELinux в Android 7.x и более ранних версиях.
Построение политики SELinux
Политика SELinux создается путем объединения основной политики AOSP с настройками для конкретных устройств. Объединенная политика затем передается компилятору политик и различным программам проверки. Настройка для конкретного устройства выполняется с помощью переменной BOARD_SEPOLICY_DIRS определенной в файле Boardconfig.mk для конкретного устройства. Эта глобальная переменная сборки содержит список каталогов, определяющих порядок поиска дополнительных файлов политики.
Например, поставщик SoC и ODM могут каждый добавить каталог, один для настроек, специфичных для SoC, а другой для настроек, специфичных для устройства, для создания окончательных конфигураций SELinux для данного устройства:
-
BOARD_SEPOLICY_DIRS += device/ SOC /common/sepolicy -
BOARD_SEPOLICY_DIRS += device/ SoC / DEVICE /sepolicy
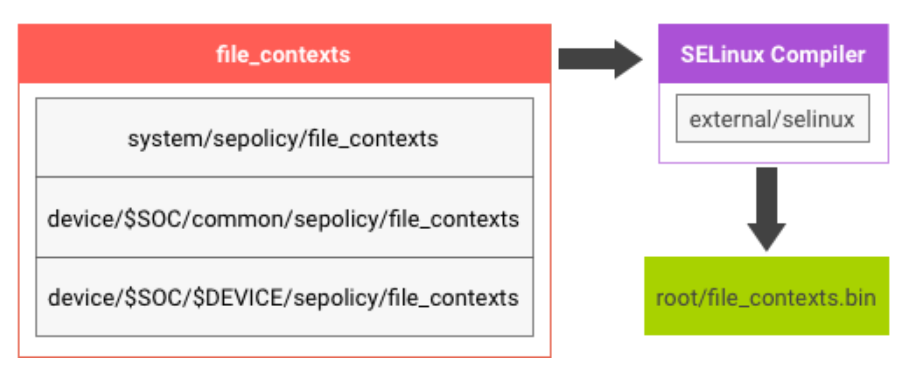
Содержимое файлов file_contexts в system/sepolicy и BOARD_SEPOLICY_DIRS объединяется для создания file_contexts.bin на устройстве:
Файл sepolicy состоит из нескольких исходных файлов:
- Простой текст
policy.confсоздается путем объединения файловsecurity_classes,initial_sids,*.te,genfs_contextsиport_contextsв указанном порядке. - Для каждого файла (например,
security_classes) его содержимое представляет собой конкатенацию файлов с тем же именем вsystem/sepolicy/иBOARDS_SEPOLICY_DIRS. -
policy.confотправляется компилятору SELinux для проверки синтаксиса и компилируется в двоичный формат какsepolicyна устройстве.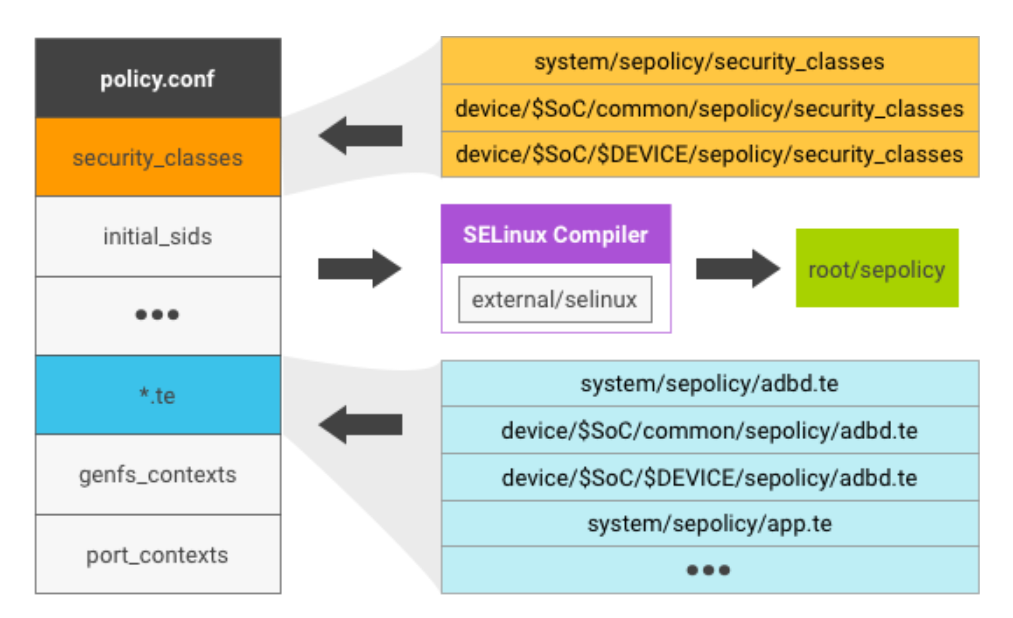
Рисунок 2 . Файл политики SELinux
файлы SELinux
После компиляции устройства Android под управлением 7.x и более ранних версий обычно содержат следующие файлы, связанные с SELinux:
-
selinux_version - sepolicy: двоичный вывод после объединения файлов политик (например,
security_classes,initial_sidsи*.te) -
file_contexts -
property_contexts -
seapp_contexts -
service_contexts -
system/etc/mac_permissions.xml
Дополнительные сведения см. в разделе Реализация SELinux .
Инициализация SELinux
Когда система загружается, SELinux находится в разрешительном режиме (а не в принудительном). Процесс инициализации выполняет следующие задачи:
- Загружает файлы
sepolicyс ramdisk в ядро через/sys/fs/selinux/load. - Переключает SELinux в принудительный режим.
- Запускает
re-exec(), чтобы применить правило домена SELinux к себе.
Чтобы сократить время загрузки, как можно скорее выполните re-exec() в процессе init .
Андроид 8.0 и выше
В Android 8.0 политика SELinux разделена на компоненты платформы и поставщика, чтобы разрешить независимые обновления политики платформы/поставщика при сохранении совместимости.
Секретная политика платформы дополнительно разделена на частную и общедоступную части платформы для экспорта определенных типов и атрибутов авторам политик поставщиков. Общедоступные типы/атрибуты платформы гарантированно будут поддерживаться как стабильные API для данной версии платформы. Совместимость с предыдущими общедоступными типами/атрибутами платформы может быть гарантирована для нескольких версий с помощью файлов отображения платформы.
Публичная политика платформы
Public sepolicy платформы включает в себя все, что определено в system/sepolicy/public . Платформа может предполагать, что типы и атрибуты, определенные общедоступной политикой, являются стабильными API для данной версии платформы. Это формирует часть политики sepolicy, которая экспортируется платформой, на которой разработчики политики поставщика (т. е. устройства) могут написать дополнительную политику для конкретного устройства.
Типы версионируются в соответствии с версией политики, для которой записываются файлы поставщиков, определяемой переменной сборки PLATFORM_SEPOLICY_VERSION . Публичная политика с поддержкой версий затем включается в политику поставщика и (в исходной форме) в политику платформы. Таким образом, окончательная политика включает в себя политику частной платформы, общедоступную политику текущей платформы, политику для конкретного устройства и общедоступную политику с версией, соответствующую версии платформы, для которой была написана политика устройства.
Частная политика платформы
Частная политика безопасности платформы включает в себя все, что определено в /system/sepolicy/private . Эта часть политики формирует только для платформы типы, разрешения и атрибуты, необходимые для функциональности платформы. Они не экспортируются авторам политик vendor/device . Авторы политик, не относящиеся к платформе, не должны создавать свои расширения политик на основе типов/атрибутов/правил, определенных в частной политике платформы. Более того, эти правила разрешено изменять или они могут исчезнуть как часть обновления только для фреймворка.
Частное сопоставление платформы
Частное сопоставление платформы включает операторы политики, которые сопоставляют атрибуты, представленные в общедоступной политике платформы предыдущих версий платформы, с конкретными типами, используемыми в текущей общедоступной политике платформы. Это гарантирует, что политика поставщика, которая была написана на основе общедоступных атрибутов платформы из предыдущих версий общедоступной политики платформы, продолжает работать. Управление версиями основано на переменной сборки PLATFORM_SEPOLICY_VERSION , установленной в AOSP для данной версии платформы. Отдельный файл сопоставления существует для каждой предыдущей версии платформы, от которой ожидается, что эта платформа примет политику поставщика. Дополнительные сведения см. в разделе Совместимость .
Андроид 11 и выше
system_ext и продуктовая политика
В Android 11 добавлены политика system_ext и политика продукта. Как и политика sepolicy платформы, политика system_ext и политика продукта разделены на общедоступную и частную политики.
Публичная политика экспортируется поставщику. Типы и атрибуты становятся стабильным API, а политика поставщика может ссылаться на типы и атрибуты в общедоступной политике. Типы управляются версиями в соответствии с PLATFORM_SEPOLICY_VERSION , и политика управления версиями включена в политику поставщика. Исходная политика включена в каждый из разделов system_ext и product.
Частная политика содержит типы, разрешения и атрибуты только для system_ext и только для продукта, необходимые для функциональности разделов system_ext и продукта. Частная политика невидима для поставщика, что означает, что эти правила являются внутренними и могут быть изменены.
system_ext и сопоставление продуктов
system_ext и product могут экспортировать назначенные им общедоступные типы в vendor. Однако ответственность за обеспечение совместимости лежит на каждом партнере. Для совместимости партнеры могут предоставить свои собственные файлы сопоставления, которые сопоставляют версионные атрибуты предыдущих версий с конкретными типами, используемыми в текущей общедоступной политике безопасности.
- Чтобы установить файл сопоставления для system_ext, поместите cil-файл, содержащий нужную информацию о сопоставлении, в
{SYSTEM_EXT_PRIVATE_SEPOLICY_DIRS}/compat/{ver}/{ver}.cil, а затем добавьтеsystem_ext_{ver}.cilвPRODUCT_PACKAGES. - Чтобы установить файл сопоставления для продукта, поместите cil-файл, содержащий нужную информацию о сопоставлении, в
{PRODUCT_PRIVATE_SEPOLICY_DIRS}/compat/{ver}/{ver}.cil, а затем добавьтеproduct_{ver}.cilвPRODUCT_PACKAGES. Обратитесь к примеру, который добавляет файл сопоставления раздела продукта устройства Redbull. - Преобразование политик в формат SELinux Common Intermediate Language (CIL), а именно:
- общедоступная политика платформы (system + system_ext + product)
- комбинированная частная + государственная политика
- политика public + vendor и
BOARD_SEPOLICY_DIRS
- Управление версиями политики, предоставляемой public как часть политики поставщика. Выполняется с помощью созданной общедоступной политики CIL для информирования объединенной политики public + vendor +
BOARD_SEPOLICY_DIRSо том, какие части должны быть преобразованы в атрибуты, которые будут связаны с политикой платформы. - Создание файла сопоставления, связывающего компоненты платформы и поставщика. Первоначально это просто связывает типы из общедоступной политики с соответствующими атрибутами в политике поставщика; позже он также послужит основой для файла, поддерживаемого в будущих версиях платформы, что обеспечит совместимость с политикой поставщика, ориентированной на эту версию платформы.
- Объединение файлов политик (описание как встроенных, так и предварительно скомпилированных решений).
- Объедините сопоставление, платформу и политику поставщика.
- Скомпилируйте выходной двоичный файл политики.
- И
/system/etc/selinux/plat_sepolicy_and_mapping.sha256и/{partition}/etc/selinux/precompiled_sepolicy.plat_sepolicy_and_mapping.sha256существуют и идентичны. - И
/system_ext/etc/selinux/system_ext_sepolicy_and_mapping.sha256, и/{partition}/etc/selinux/precompiled_sepolicy.system_ext_sepolicy_and_mapping.sha256не существуют. Или оба существуют и идентичны. - И
/product/etc/selinux/product_sepolicy_and_mapping.sha256, и/{partition}/etc/selinux/precompiled_sepolicy.product_sepolicy_and_mapping.sha256не существуют. Или оба существуют и идентичны.
Построение политики SELinux
Политика SELinux в Android 8.0 создается путем объединения частей из /system и /vendor . Логика для правильной настройки находится в /platform/system/sepolicy/Android.mk .
Политика существует в следующих местах:
| Расположение | Содержит |
|---|---|
system/sepolicy/public | API-интерфейс sepolicy платформы |
system/sepolicy/private | Детали реализации платформы (поставщики могут игнорировать) |
system/sepolicy/vendor | Файлы политики и контекста, которые могут использовать поставщики (при желании поставщики могут игнорировать) |
BOARD_SEPOLICY_DIRS | Политика поставщика |
BOARD_ODM_SEPOLICY_DIRS (Android 9 и выше) | ОДМ sepolicy |
SYSTEM_EXT_PUBLIC_SEPOLICY_DIRS (Android 11 и выше) | API-интерфейс sepolicy System_ext |
SYSTEM_EXT_PRIVATE_SEPOLICY_DIRS (Android 11 и выше) | Детали реализации System_ext (поставщики могут игнорировать) |
PRODUCT_PUBLIC_SEPOLICY_DIRS (Android 11 и выше) | API-интерфейс sepolicy продукта |
PRODUCT_PRIVATE_SEPOLICY_DIRS (Android 11 и выше) | Детали реализации продукта (поставщики могут игнорировать) |
Система сборки принимает эту политику и создает компоненты политики system, system_ext, product, vendor и odm в соответствующем разделе. Шаги включают в себя:
Предварительно скомпилированная политика SELinux
Прежде чем init включит SELinux, init собирает все CIL-файлы из разделов ( system , system_ext , product , vendor и odm ) и компилирует их в двоичную политику, формат которой можно загрузить в ядро. Поскольку компиляция занимает время (обычно 1-2 секунды), файлы CIL предварительно компилируются во время сборки и помещаются либо в /vendor/etc/selinux/precompiled_sepolicy , либо в /odm/etc/selinux/precompiled_sepolicy precompiled_sepolicy вместе с хэшами sha256. входных файлов CIL. Во время выполнения init проверяет, был ли обновлен какой-либо файл политики, сравнивая хэши. Если ничего не изменилось, init загружает предварительно скомпилированную политику. Если нет, то init компилируется на лету и использует его вместо предварительно скомпилированного.
В частности, предварительно скомпилированная политика используется, если выполняются все следующие условия. Здесь {partition} представляет раздел, в котором существует предварительно скомпилированная политика: vendor или odm .
Если какой-либо из них отличается, init возвращается к пути компиляции на устройстве. Подробнее см. в system/core/init/selinux.cpp .

