為配合主幹穩定開發模型,並確保生態系統的平台穩定性,我們將於 2026 年起,在第 2 季和第 4 季將原始碼發布至 AOSP。如要建構及貢獻 AOSP,建議使用 android-latest-release,而非 aosp-main。android-latest-release 資訊清單分支版本一律會參照推送至 AOSP 的最新版本。詳情請參閱「Android 開放原始碼計畫變更」一文。
 Google uses AI technology to translate content into your preferred language. AI translations can contain errors.
Google uses AI technology to translate content into your preferred language. AI translations can contain errors.
裝置 ID 組合引擎
透過集合功能整理內容
你可以依據偏好儲存及分類內容。
裝置 ID 組成引擎 (DICE) 是可信賴運算組織 (TCG) 規格,已納入 Android。這項功能會為啟動順序期間載入的每個韌體建立一組不可變動的高強度密碼編譯身分。這些身分可供遠端驗證裝置的安全性狀態,只有入侵 ROM 才能規避驗證。
DICE 衍生程序
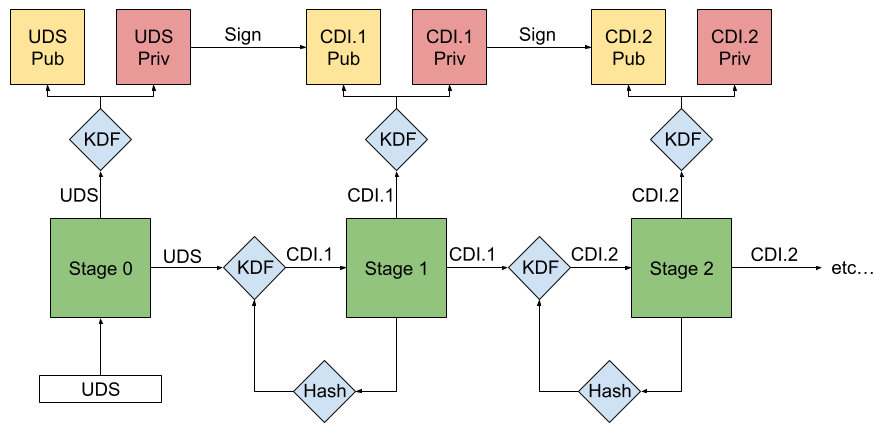
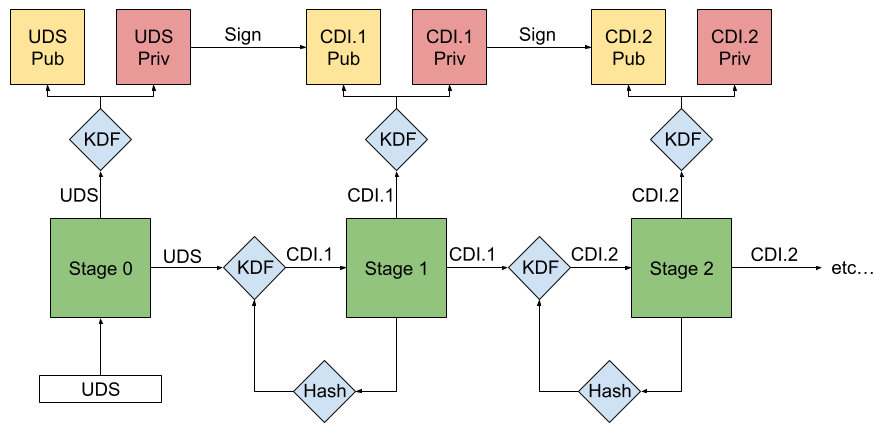
圖 1. 簡化 DICE 衍生程序。
DICE 衍生程序可確保韌體映像檔的任何變更,都會導致該階段和後續每個階段產生新的專屬 ID。這是因為每個載入的韌體階段都會測量並認證下一個階段,產生專屬 ID 和相關聯的金鑰,防止繞過或竄改。唯讀記憶體 (ROM) 會使用金鑰衍生函式 (KDF) 處理測量、設定和裝置專屬密碼 (UDS),以衍生要載入下一個階段的密碼。這個密碼稱為複合裝置 ID (CDI)。
第 0 階段:初始化
DICE 程序會先由晶片組的 ROM 從不可變動的資料庫 (通常是熔絲) 載入 UDS,在晶片生產過程中,系統會以密碼編譯隨機值安全地佈建這項 UDS。讀取 UDS 後,ROM 會使用與供應商相關的硬體鎖定機制 (例如閂鎖),鎖定 UDS 存取權,直到下次啟動為止。
階段 1:初始金鑰衍生
ROM 會將 UDS 做為金鑰衍生函式 (KDF) 的輸入內容,產生可唯一識別該裝置的永久非對稱金鑰組。這項功能會測量下一個韌體階段,包括開機環境的中繼資料,例如是否已啟用安全啟動。接著,ROM 會在 KDF 中合併 UDS、韌體測量結果和設定資料,衍生出第一個 CDI,並以密碼的形式傳遞至下一個階段。
階段 2 至 n:遞迴金鑰衍生
然後重複上述程序。在後續所有階段中,前一階段的 CDI 會做為新 KDF 的輸入內容。這個 KDF 會使用 CDI 和下一個韌體映像檔的雜湊值,產生新的衍生 CDI。每個階段都會產生自己的金鑰配對,並用來簽署含有階段專屬測量結果和其他相關中繼資料的憑證。
這個頁面中的內容和程式碼範例均受《內容授權》中的授權所規範。Java 與 OpenJDK 是 Oracle 和/或其關係企業的商標或註冊商標。
上次更新時間:2025-12-03 (世界標準時間)。
[[["容易理解","easyToUnderstand","thumb-up"],["確實解決了我的問題","solvedMyProblem","thumb-up"],["其他","otherUp","thumb-up"]],[["缺少我需要的資訊","missingTheInformationINeed","thumb-down"],["過於複雜/步驟過多","tooComplicatedTooManySteps","thumb-down"],["過時","outOfDate","thumb-down"],["翻譯問題","translationIssue","thumb-down"],["示例/程式碼問題","samplesCodeIssue","thumb-down"],["其他","otherDown","thumb-down"]],["上次更新時間:2025-12-03 (世界標準時間)。"],[],[]]