本頁面說明裝置的建議啟動流程,如圖 1 所示:
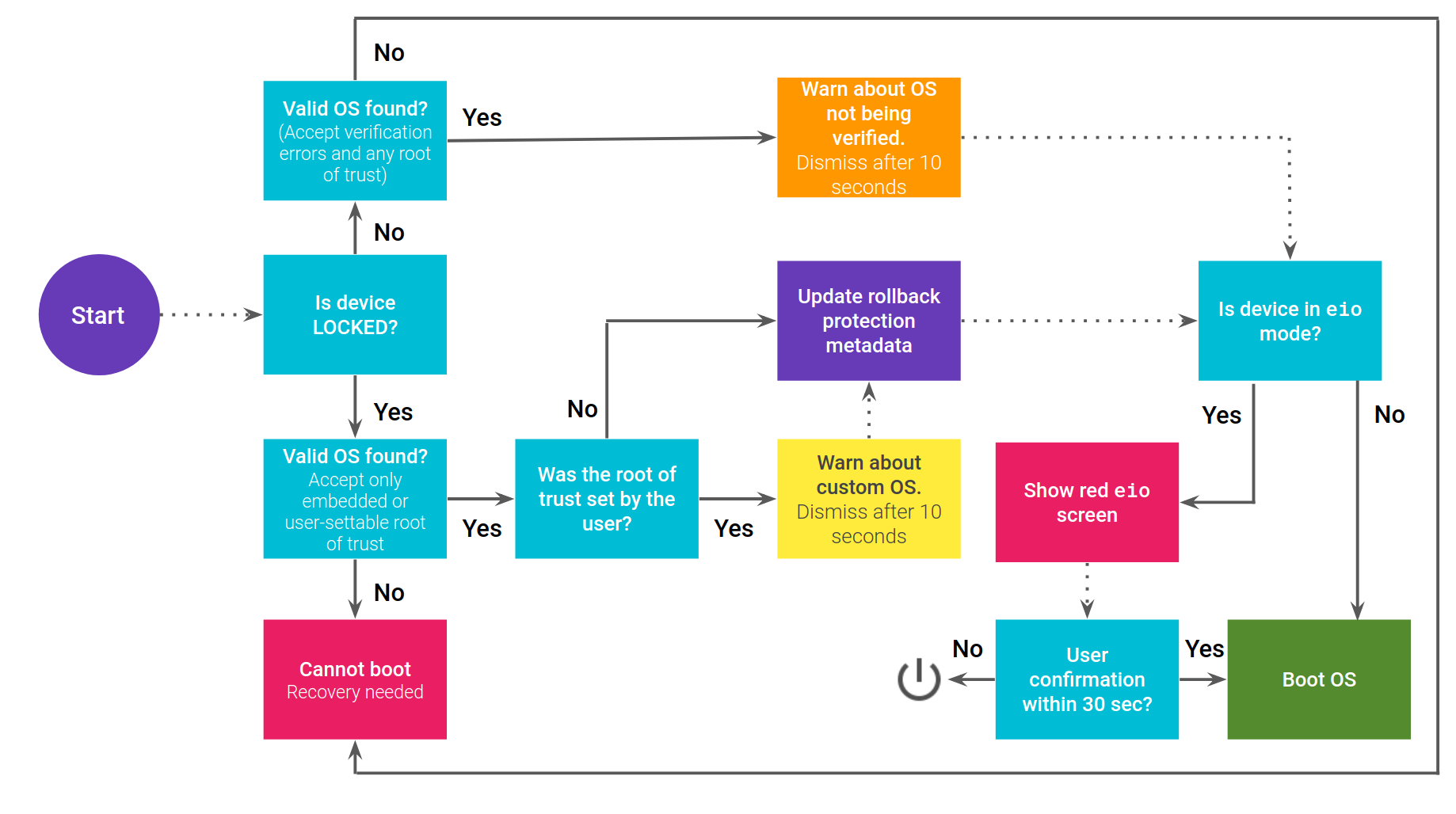
圖 1. 驗證開機程序流程。
A/B 裝置的流程
如果裝置使用 A/B,啟動流程會稍有不同。必須先使用 Boot Control HAL 將要啟動的插槽標示為 SUCCESSFUL,才能更新回溯保護中繼資料。
如果平台更新失敗 (未標示 SUCCESSFUL),A/B 堆疊會回復到另一個插槽,其中仍有先前的 Android 版本。不過,如果已設定復原保護機制中繼資料,由於復原保護機制,先前版本將無法啟動。
向使用者說明驗證開機程序狀態
判斷裝置的啟動狀態後,請將該狀態告知使用者。如果裝置沒有任何問題,請繼續操作,不要顯示任何內容。已驗證啟動問題可分為以下幾類:
- 黃色:警告畫面,適用於設定自訂信任根的已鎖定裝置
- 橘色:未解鎖裝置的警告畫面
- 紅色 (
eio):dm-verity 損毀的警告畫面 - 紅色 (找不到 OS):找不到有效的 OS
已鎖定且具有自訂信任根的裝置
如果裝置已鎖定、已設定自訂信任根,且映像檔已使用這個自訂信任根簽署,則每次開機時都會顯示黃色畫面。黃色畫面會在十秒後消失,裝置會繼續啟動。如果使用者按下電源鍵,「按下電源鍵即可暫停」文字會變更為「按下電源鍵即可繼續」,且螢幕不會關閉 (裝置可能會調暗或關閉螢幕,避免烙印)。再次按下按鈕即可關閉畫面,手機會繼續啟動。
對於 hex-number,請使用用於驗證的公開金鑰 libavb 代表項目的 sha256 前八位數,例如 d14a028c。
建議的文字:
裝置正在載入其他作業系統。
在其他裝置上點選這個連結:
g.co/ABH
OS 指紋:hex-number
按下電源鍵即可暫停
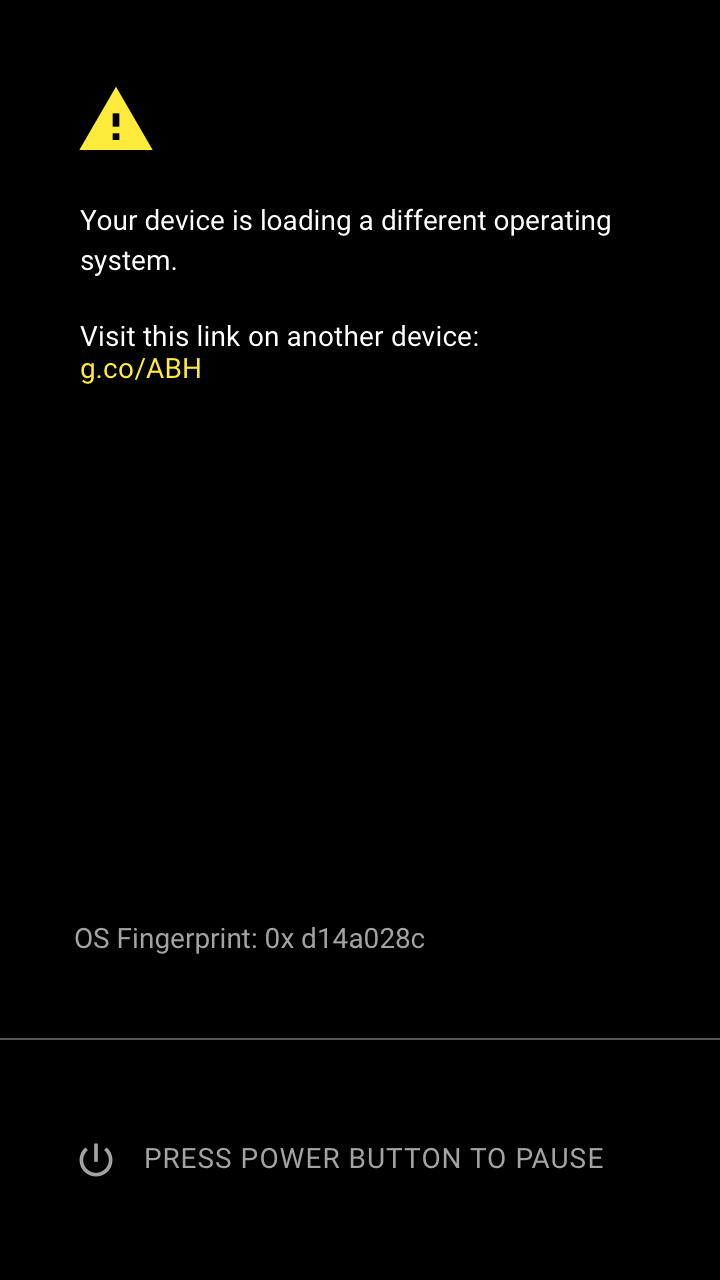
圖 2. YELLOW 畫面範例。
已解鎖的裝置
如果裝置已解鎖,每次啟動時都會顯示橘色畫面。橘色畫面會在十秒後消失,裝置會繼續啟動。如果使用者按下電源鍵,「按下電源鍵即可暫停」文字會變更為「按下電源鍵即可繼續」,且畫面不會關閉 (裝置可能會視需要調暗及/或關閉螢幕,以防螢幕烙印或類似情況)。如果再次按下,畫面就會關閉,手機會繼續啟動。
對於 hex-number,請使用用於驗證的公開金鑰 libavb 代表項目的 sha256 前八位數,例如 d14a028c。
建議的文字:
本裝置的系統啟動載入程式已解鎖,因此我們目前無法保證軟體完整性。Any data stored on the device might be available to attackers. 因此請勿將私密資料儲存在裝置上。
在其他裝置上點選這個連結:
g.co/ABH
ID:hex-number
按下電源鍵可暫停。
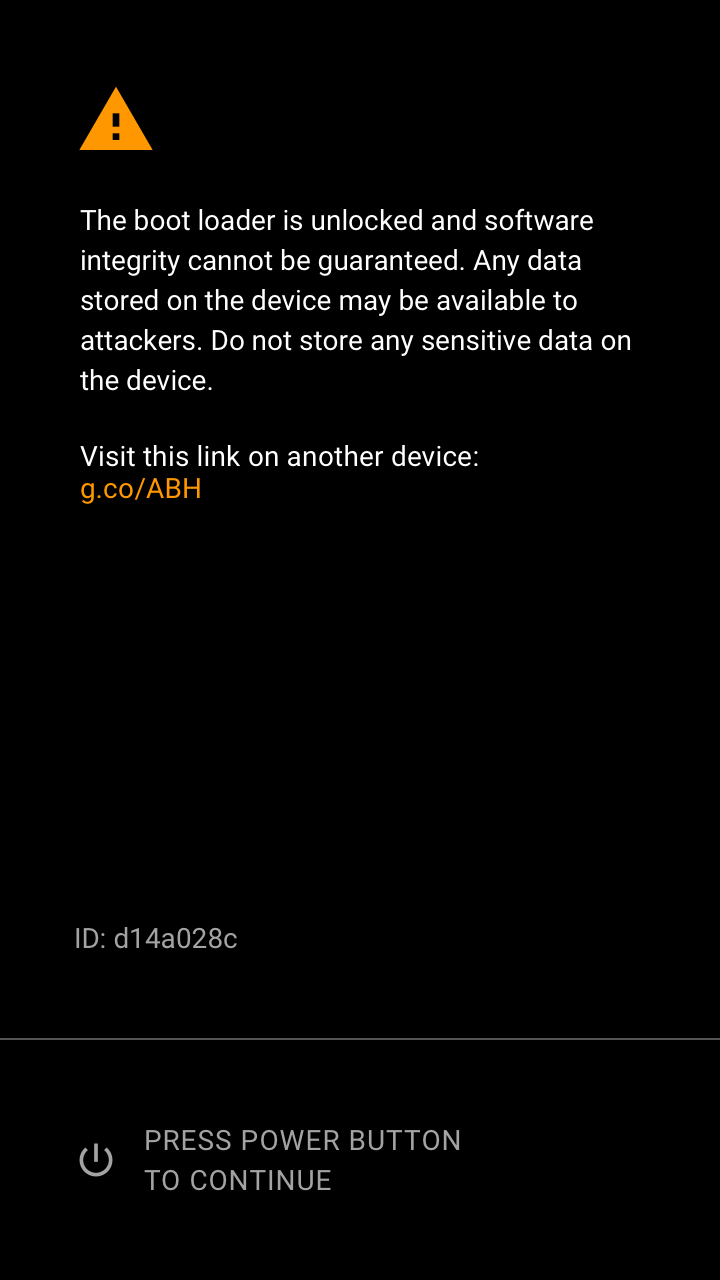
圖 3. 範例:ORANGE 畫面。
dm-verity 損毀
如果找到有效的 Android 版本,且裝置處於 eio dm-verity 模式,就會顯示紅色 eio 畫面。使用者必須按下電源鍵才能繼續。如果使用者在 30 秒內未確認警告畫面,裝置就會關機 (保護螢幕免於烙印並節省電力)。
建議的文字:
裝置已損壞。因此無法信任,也可能無法正常運作。
在其他裝置上點選這個連結:
g.co/ABH
按下電源鍵繼續操作。
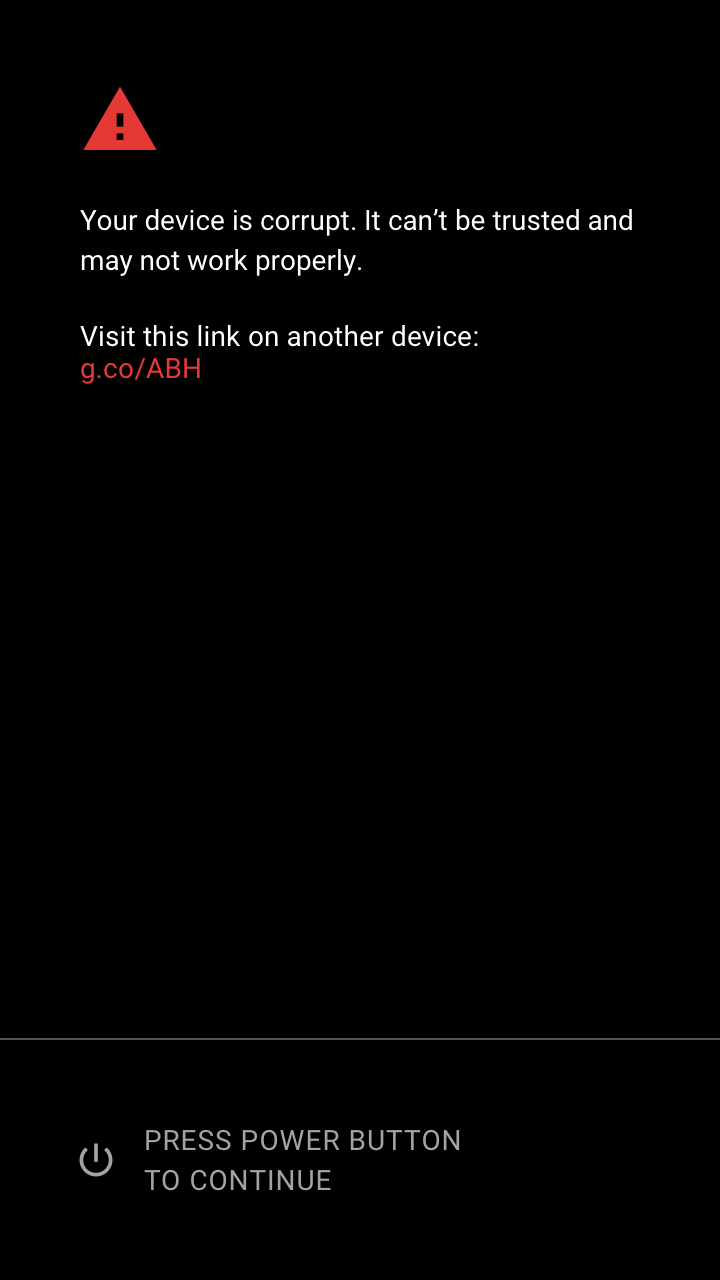
圖 4. RED eio 畫面範例。
找不到有效的作業系統
如果找不到有效的 Android 版本,請顯示紅色畫面。裝置無法繼續啟動。如果使用者在 30 秒內未確認警告畫面,裝置就會關機,避免螢幕烙印並節省電力。
對於 hex-number,請使用用於驗證的公開金鑰 libavb 代表項目的前八位數 sha256,例如 d14a028c。
建議的文字:
找不到有效的作業系統。裝置無法開機。
在其他裝置上點選這個連結:
g.co/ABH
ID:hex-number
按下電源鍵關機。
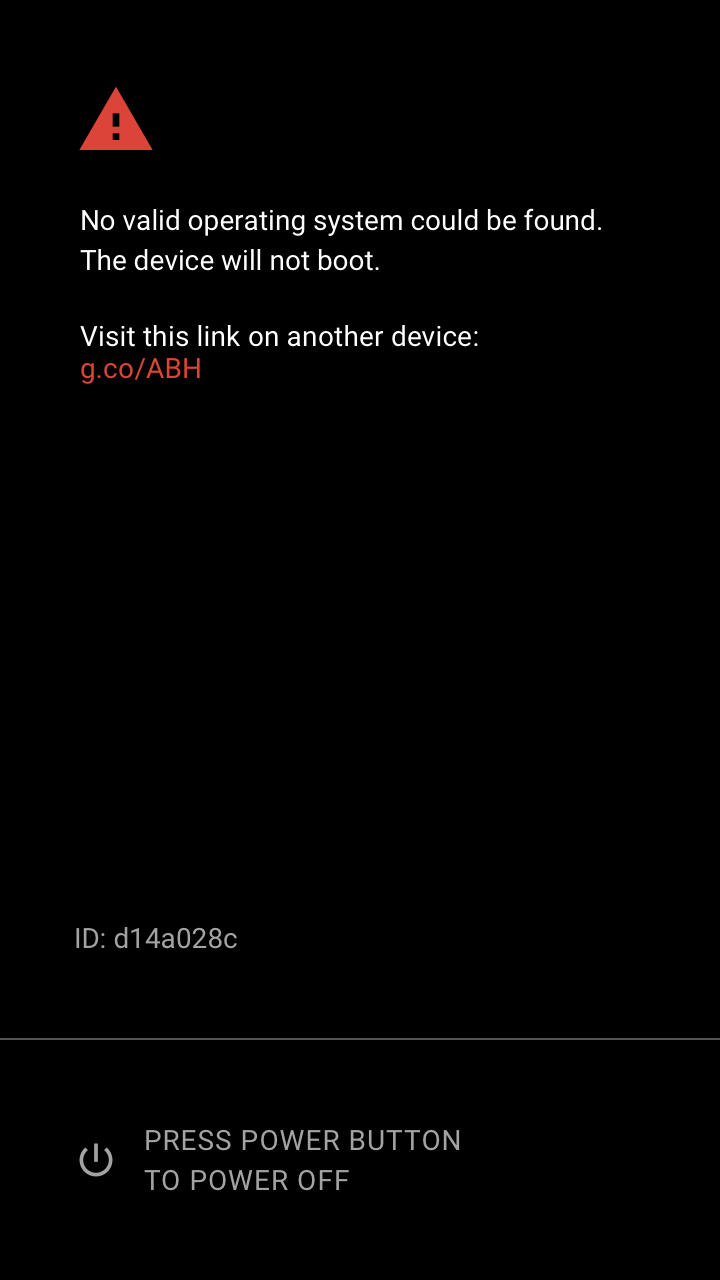
圖 5. RED 畫面範例。
確認解鎖
在透過 Fastboot 介面執行 fastboot flashing unlock 指令後,顯示解鎖確認畫面。焦點一開始會放在「不要解鎖」。如果使用者在 30 秒內未與警告畫面互動,該畫面就會消失,且指令會失敗。
建議的文字:
解鎖系統啟動載入程式後,您就能在這支手機上安裝自訂作業系統軟體。自訂作業系統的測試程度不如原始作業系統,可能會導致手機和已安裝的應用程式無法正常運作。
自訂 OS 無法保證軟體完整性,且系統啟動載入程式解鎖時,手機上的資料可能會有風險。
為防止未經授權存取個人資料,解鎖系統啟動載入程式時,系統也會刪除手機上的所有個人資料。
按下音量鍵選取是否要解鎖開機載入程式,然後按下電源鍵繼續操作。
不要解鎖系統啟動載入程式,然後重新啟動手機。
解鎖系統啟動載入程式。
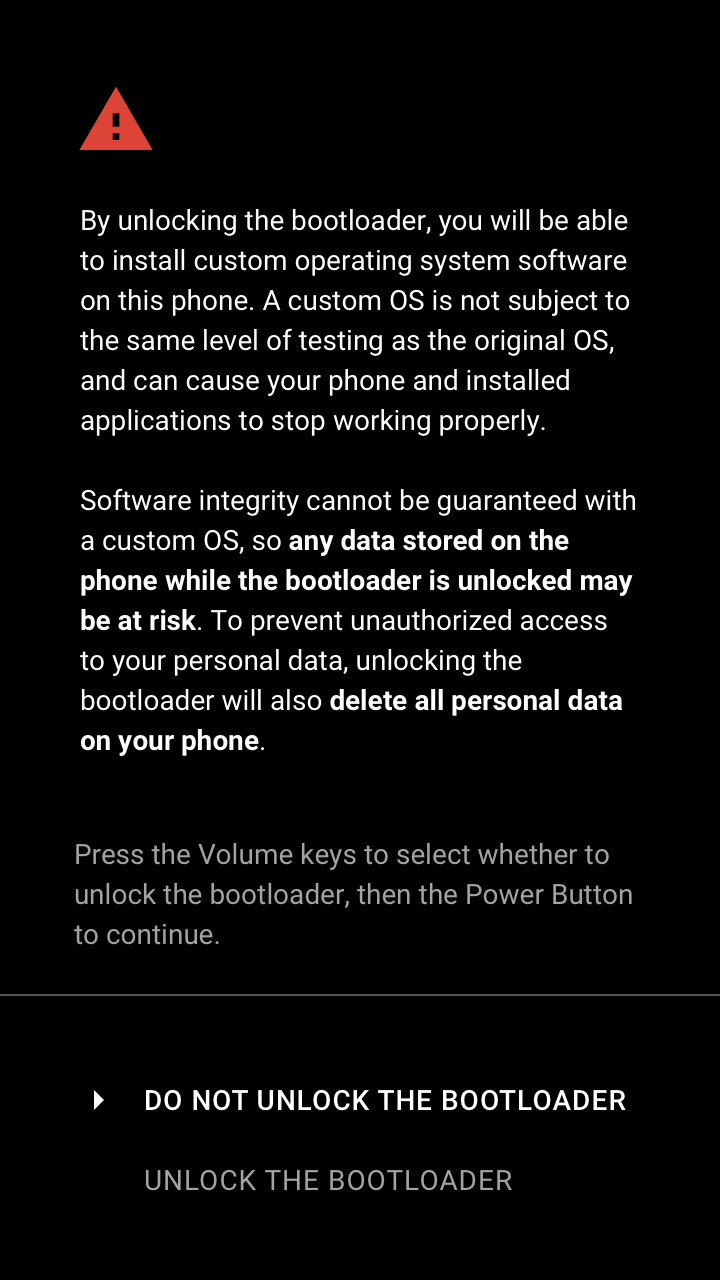
圖 6. 解鎖確認畫面範例。
確認鎖定
透過 Fastboot 介面執行 fastboot flashing
lock 指令時,顯示鎖定確認畫面。焦點一開始會放在「不要鎖定」上。如果使用者在 30 秒內未與警告畫面互動,畫面就會消失,且指令會失敗。
文字:
鎖定系統啟動載入程式後,您就無法在這部手機上安裝自訂作業系統軟體。
為防止未經授權存取您的個人資料,鎖定系統啟動載入程式時,系統也會刪除手機上的所有個人資料。
按下音量鍵選取是否要鎖定開機載入程式,然後按下電源鍵繼續。
不要鎖定系統啟動載入程式,然後重新啟動手機。
鎖定系統啟動載入程式。
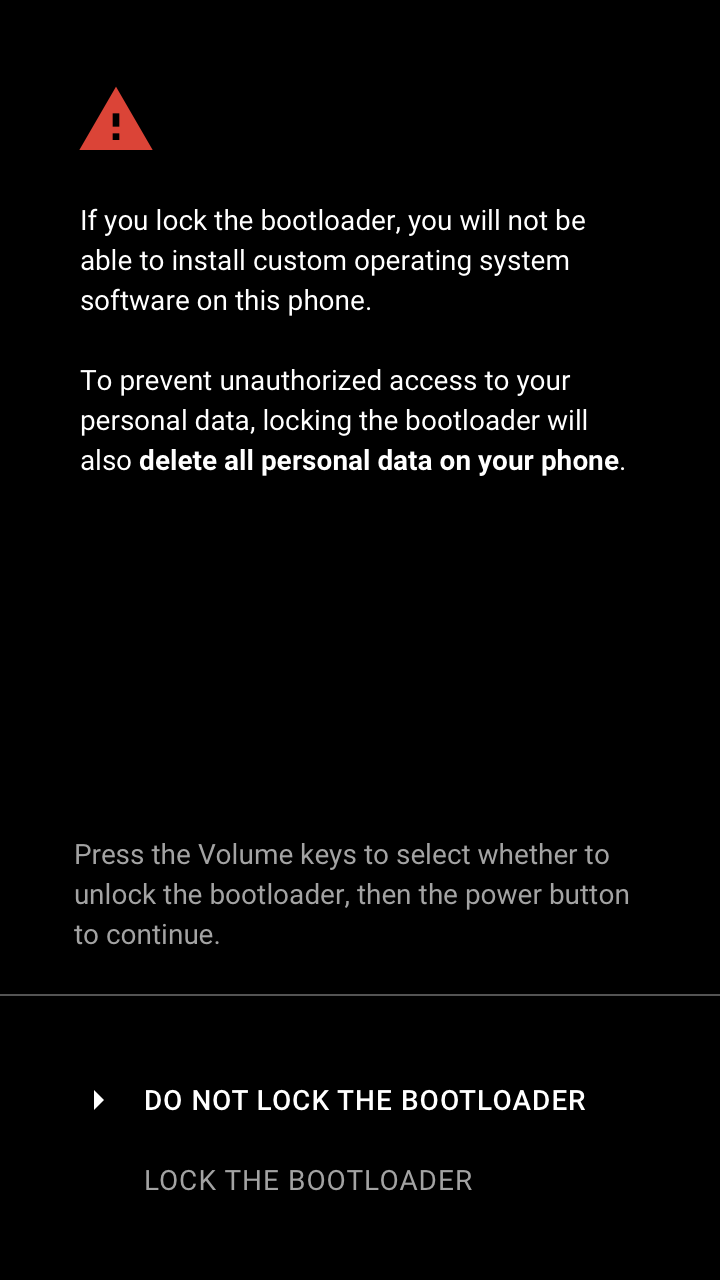
圖 7. 鎖定確認裝置警告畫面。
向 Android 傳達驗證開機程序狀態
系統啟動載入程式會透過核心指令參數,或 Android 12 以上版本的啟動設定,將「已驗證啟動」狀態傳達給 Android。開機載入程式會將 androidboot.verifiedbootstate 選項設為下列其中一個值:
green(如果裝置是LOCKED,且未使用使用者可設定的信任根)yellow如果裝置是LOCKED,且使用可由使用者設定的信任根orange如果裝置UNLOCKED
androidboot.veritymode 選項會根據開機載入程式處理 dm-verity 錯誤的狀態,設為 eio 或 restart。詳情請參閱「處理驗證錯誤」。

