本頁面說明如何啟用以車輛為基礎的綁定加密種子功能。
總覽
車輛綁定種子功能的主要目標,是透過保護車輛內娛樂資訊系統 (IVI) 系統中的資料,進一步保護使用者的隱私權。這項操作是透過將儲存空間加密金鑰繫結至其他電子控制單元 (ECU) 來完成,這樣一來,如果將 IVI 移除並放置在其他車輛 (或在測試台上執行),就無法解密 IVI 上的加密使用者資料。
為了將檔案加密金鑰繫結,Vold 會將車輛專屬的種子與金鑰加密金鑰衍生方法混合,以便將金鑰與車輛繫結。種子為位元組陣列,由原始設備製造商 (STORAGE_ENCRYPTION_BINDING_SEED) 公開為新的車輛硬體抽象層 (VHAL) 屬性。這項屬性的權限受到限制,因此只有具備權限的系統守護程序才能查詢。
架構圖
下圖說明車輛綁定整合的架構:

圖 1. 車輛綁定架構。
啟用車輛繫結
必須明確啟用儲存空間加密功能與車輛的繫結,且必須執行恢復原廠設定才能開啟或關閉。也就是說,無線更新 (OTA) 無法在未清除裝置資料的情況下啟用這項功能。如果原始設備製造商 (OEM) 也將裝置恢復原廠設定,則可選擇在升級時啟用這項功能。例如在服務拜訪時。
只要在供應商提供的車輛 HAL 中支援 STORAGE_ENCRYPTION_BINDING_SEED 屬性,即可啟用這項功能。這個屬性會保留長度為 16 位元組的位元組字串,並預期會在 IVI 以外的 ECU 上保留。這個屬性最初是由 Android Automotive OS (AAOS) 設定,並使用加密安全隨機號碼產生器 (CSRNG) 產生。AAOS 會在後續啟動時讀取該屬性。
VHAL 儲存 STORAGE_ENCRYPTION_BINDING_SEED 的值的方式會因供應商而異。我們提供以下一般建議,協助您保護種子:
- (建議) 種子會由車輛中的 ECU 儲存,且受到良好的物理保護。如果沒有,從車輛中取出 IVI 和 ECU 就會很簡單。
- (建議) IVI 和 ECU 應相互驗證,交換種子,以防 ECU 偽造種子要求。
- (建議) 請使用安全管道傳送種子,以防 CAN 匯流排嗅探。
此外,請新增以下內容,確保供應商 init.target.rc 在 late-fs 前 mount_all --late:
# feed vehicle binding seed to vold
exec_start vold_seed_binding車輛 HAL 應在 early_hal 中啟動,而非 hal now。/data 分區尚未掛載,因此無法在 early-hal 中存取任何 persist.* 系統屬性。
設定以車輛為基礎的繫結
如果 ECU 種子不相符,裝置會重新啟動至復原模式,並提示使用者清除 /data 分區或重試。
您可以在 builtins.cpp 中變更提示和清除資料的行為:
- 將
prompt_and_wipe_data變更為wipe_data。裝置會在沒有提示的情況下清除資料,然後重新啟動。 - 提示訊息包含在 recovery.cpp 中。
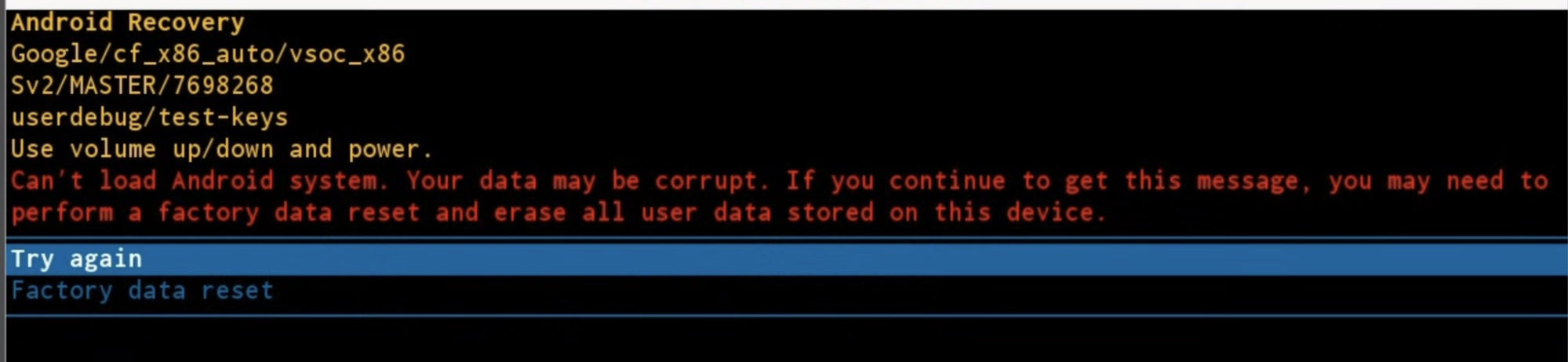
圖 2. 提示訊息。
測試車輛式繫結
模擬測試
packages/services/Car/cpp/security/vehicle_binding_util/tests 會提供模擬測試。
如要執行這項模擬測試,請按照下列步驟操作:
attest libvehicle_binding_util_test
整合測試
packages/services/Car/cpp/security/vehicle_binding_util/tests 會提供 atest 測試。
如要執行這項整合測試:
atest vehicle_binding_integration_test

