На устройствах со сканером отпечатков пальцев пользователи могут зарегистрировать один или несколько отпечатков пальцев и использовать их для разблокировки устройства и выполнения других задач. Android использует язык определения интерфейса оборудования для отпечатков пальцев (HIDL) для подключения к библиотеке производителя и оборудованию для считывания отпечатков пальцев (например, сканеру отпечатков пальцев).
Для реализации Fingerprint HIDL необходимо реализовать IBiometricsFingerprint.hal в библиотеке, специфичной для поставщика.
Сопоставление отпечатков пальцев
Сканер отпечатков пальцев устройства обычно находится в режиме ожидания. Однако в ответ на запрос authenticate или enroll сканер отпечатков пальцев реагирует на касание (экран также может активироваться при касании сканера отпечатков пальцев пользователем). Общая схема сопоставления отпечатков пальцев включает следующие этапы:
- Пользователь прикладывает палец к сканеру отпечатков пальцев.
- Библиотека поставщика определяет, есть ли совпадение отпечатков пальцев в текущем наборе зарегистрированных шаблонов отпечатков пальцев.
- Результаты сопоставления передаются в
FingerprintService.
Этот процесс предполагает, что отпечаток пальца уже зарегистрирован на устройстве, то есть, библиотека поставщика зарегистрировала шаблон для отпечатка пальца. Подробнее см. в разделе «Аутентификация» .
Архитектура
Fingerprint HAL взаимодействует со следующими компонентами.
-
BiometricManagerвзаимодействует напрямую с приложением в процессе приложения. Каждое приложение имеет экземплярIBiometricsFingerprint.hal -
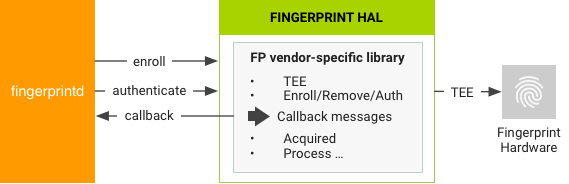
FingerprintServiceработает в системном процессе, который обеспечивает связь с HAL-сервером отпечатков пальцев. - Fingerprint HAL — это реализация интерфейса IBiometricsFingerprint HIDL на C/C++. Она содержит библиотеку, специфичную для конкретного производителя, которая взаимодействует с аппаратным обеспечением конкретного устройства.
- Компоненты Keystore API и KeyMint (ранее Keymaster) обеспечивают аппаратную криптографию для безопасного хранения ключей в защищенной среде, такой как доверенная среда выполнения (TEE).
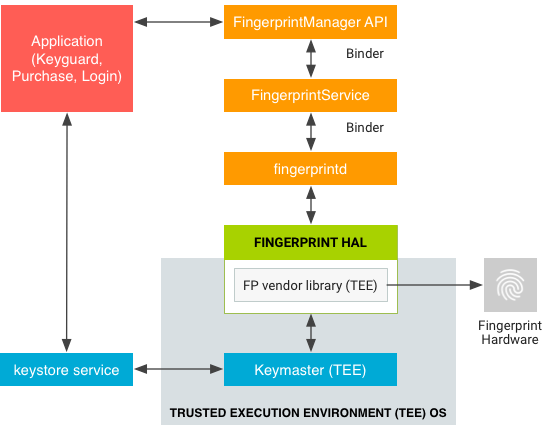
Реализация HAL, специфичная для поставщика, должна использовать протокол связи, требуемый TEE. Необработанные изображения и обработанные характеристики отпечатков пальцев не должны передаваться в ненадёжную память. Все подобные биометрические данные должны храниться на защищённом оборудовании, таком как TEE. Получение прав root не должно приводить к компрометации биометрических данных.
FingerprintService и fingerprintd выполняют вызовы через Fingerprint HAL к библиотеке поставщика для регистрации отпечатков пальцев и выполнения других операций.
Руководящие принципы реализации
Следующие рекомендации HAL по отпечаткам пальцев призваны гарантировать, что данные об отпечатках пальцев не будут утекать и будут удалены, когда пользователь отключается от устройства:
- Необработанные данные отпечатков пальцев или их производные (например, шаблоны) ни при каких обстоятельствах не должны быть доступны извне драйвера датчика или TEE. Если оборудование поддерживает TEE, доступ к нему должен быть ограничен TEE и защищён политикой SELinux. Канал последовательного периферийного интерфейса (SPI) должен быть доступен только TEE, а для всех файлов устройства должна быть предусмотрена явная политика SELinux.
- Получение, регистрация и распознавание отпечатков пальцев должны происходить внутри TEE.
- Только зашифрованная форма данных отпечатков пальцев может храниться в файловой системе, даже если сама файловая система зашифрована.
- Шаблоны отпечатков пальцев должны быть подписаны закрытым ключом, привязанным к устройству. Для AES (Advanced Encryption Standard) шаблон должен быть подписан как минимум абсолютным путём в файловой системе, группой и идентификатором пальца, чтобы файлы шаблонов нельзя было использовать на другом устройстве или для кого-либо, кроме пользователя, зарегистрировавшего их на том же устройстве. Например, копирование данных отпечатков пальцев другого пользователя на то же устройство или с другого устройства не должно работать.
- Реализации должны либо использовать путь в файловой системе, предоставленный функцией
setActiveGroup(), либо предоставлять способ удаления всех данных шаблона пользователя при удалении пользователя. Настоятельно рекомендуется хранить файлы шаблонов отпечатков пальцев в зашифрованном виде по указанному пути. Если это невозможно из-за требований к хранилищу TEE, разработчик должен добавить хуки, обеспечивающие удаление данных при удалении пользователя.
Методы дактилоскопии
Интерфейс Fingerprint HIDL содержит следующие основные методы в IBiometricsFingerprint.hal .
| Метод | Описание |
|---|---|
enroll() | Переключает конечный автомат HAL на запуск сбора и сохранения шаблона отпечатка пальца. После завершения регистрации или по истечении тайм-аута конечный автомат HAL возвращается в состояние ожидания. |
preEnroll() | Генерирует уникальный токен, указывающий на начало регистрации отпечатка пальца. Предоставляет токен функции enroll , чтобы убедиться в наличии предварительной аутентификации, например, по паролю. Для предотвращения подделки токен запаковывается после подтверждения учётных данных устройства. Необходимо проверить токен во время регистрации, чтобы убедиться в его действительности. |
getAuthenticatorId() | Возвращает токен, связанный с текущим набором отпечатков пальцев. |
cancel() | Отменяет ожидающие операции регистрации или аутентификации. Конечный автомат HAL возвращается в состояние ожидания. |
enumerate() | Синхронный вызов для перечисления всех известных шаблонов отпечатков пальцев. |
remove() | Удаляет шаблон отпечатка пальца. |
setActiveGroup() | Ограничивает операцию HAL набором отпечатков пальцев, принадлежащих указанной группе, идентифицируемой идентификатором группы (GID). |
authenticate() | Аутентифицирует операцию, связанную с отпечатком пальца (идентифицируется идентификатором операции). |
setNotify() | Регистрирует пользовательскую функцию, получающую уведомления от HAL. Если конечный автомат HAL находится в состоянии занятости, функция блокируется до тех пор, пока HAL не выйдет из этого состояния. |
postEnroll() | Завершает операцию регистрации и отменяет сгенерированный вызов preEnroll() . Этот вызов должен быть выполнен в конце сеанса многопальцевой регистрации, чтобы указать, что добавление дополнительных пальцев невозможно. |
Более подробную информацию об этом можно найти в комментариях в IBiometricsFingerprint.hal .

