The MAC randomization feature lets devices use a randomized MAC address when connecting to a Wi-Fi network. For implementation instructions, see Implement MAC randomization. This page describes the behavior of MAC randomization in Android.
When your device connects to a Wi-Fi network or an access point, it uses MAC addresses. Because these MAC addresses are transmitted without encryption, they can be captured and used to potentially track a user's location. Historically, devices use the factory MAC address to associate to a Wi-Fi network. The factory MAC address is globally unique and static, letting the device be tracked and individually identified.
The MAC randomization feature increases user privacy by using a randomized MAC address when connecting to a Wi-Fi network.
MAC addresses are 48 bits long and usually represented by 12 hex digits
(6 octets as each octet is 8 bits) such as 00:11:22:AA:BB:CC. The MAC
randomization feature randomizes the address by setting the locally
administered bit to 1, and the unicast bit to 0. The other 46 bits are
randomized.
For devices running Android 10 or higher, the framework uses a randomized MAC address by default. You can enable or disable MAC randomization for individual networks through an option in the Network details screen in Settings, as shown in Figure 1. If you disable MAC randomization for a network, the framework uses the factory MAC address (globally unique address).
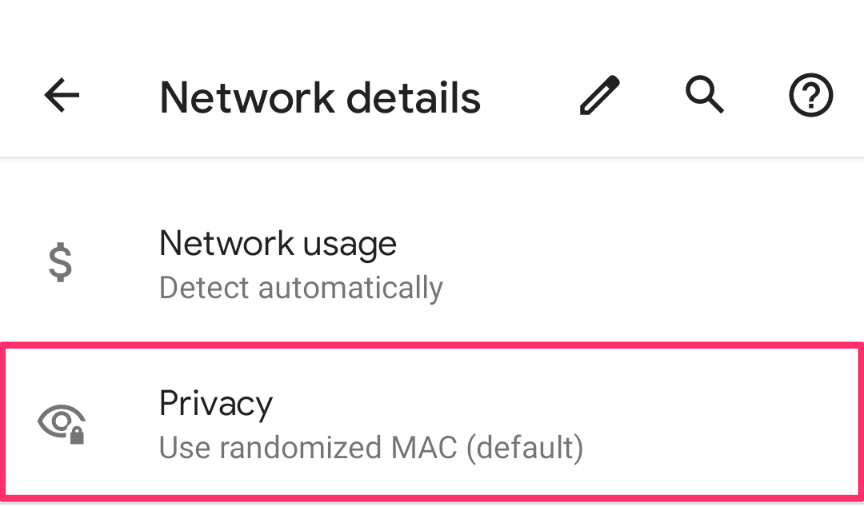
Figure 1. MAC randomization option.
MAC randomization types
The Android framework uses two types of MAC randomization: persistent randomization and non-persistent randomization. If the user disables MAC randomization, the factory MAC address is used.
Android determines which MAC randomization type to use when your device associates with a Wi-Fi network. By default, Android uses persistent randomization. Starting in Android 12, Android uses non-persistent randomization in these situations:
- A network suggestion app specifies that non-persistent randomization
be used for the network through the
WifiNetworkSuggestion.Builder#setMacRandomizationSettingAPI. - The network is an open network that hasn't encountered a captive portal and
the
config_wifiAllowEnhancedMacRandomizationOnOpenSsidsoverlay is set totrue. This overlay is disabled (set tofalse) by default.
Persistent randomization
Android uses the persistent randomization type by default when MAC randomization is enabled. Android generates a persistent randomized MAC address based on the network profile's parameters, including SSID, security type, or FQDN (for Passpoint networks). This MAC address remains the same until a factory reset. The MAC address doesn't get re-randomized if you forget and re-add the Wi-Fi network, because the MAC address depends on the network profile's parameters.
Persistent MAC addresses are necessary when networks rely on MAC address persistence to provide useful functionality. For example, they can help remember a device and let you bypass the login screen as expected, or enable parental controls.
For Android 10 and 11, the framework uses persistent randomization for all networks when MAC randomization is enabled.
Non-persistent randomization
With non-persistent randomization, which is used for some networks in Android 12 or higher, the Wi-Fi module re-randomizes the MAC address at the start of every connection, or the framework uses the existing randomized MAC address to connect to the network. The Wi-Fi module re-randomizes the MAC address in these situations:
- The DHCP lease duration has expired and more than 4 hours have elapsed since the device last disconnected from this network.
- The current randomized MAC for the network profile was generated more than 24 hours ago. MAC address re-randomization only happens at the start of a new connection. Wi-Fi won't actively disconnect to re-randomize a MAC address.
If none of these situations apply, the framework uses the previously randomized MAC address to connect to the network.
Developer option for non-persistent randomization
For devices running Android 11 or higher, you can enable non-persistent MAC randomization globally for all Wi-Fi networks (that have MAC randomization enabled) through the developer options screen. You can find the option to enable non-persistent MAC randomization for all profiles at Settings > Developer Options > Wi-Fi non-persistent MAC randomization.
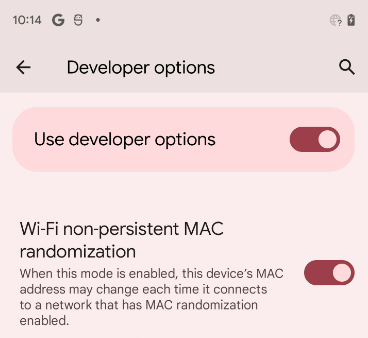
Figure 2. Wi-Fi non-persistent MAC randomization option.
