Android 虛擬化架構 (AVF) 提供安全且私密的程式碼執行環境。AVF 非常適合注重安全性的用途,因為與 Android 應用程式沙箱提供的保證相比,AVF 可提供更強大,甚至是經過正式驗證的隔離保證。Android 提供實作 AVF 所需所有元件的參考實作方式。AVF 僅支援 ARM64 裝置。圖 1 顯示 AVF 的架構:
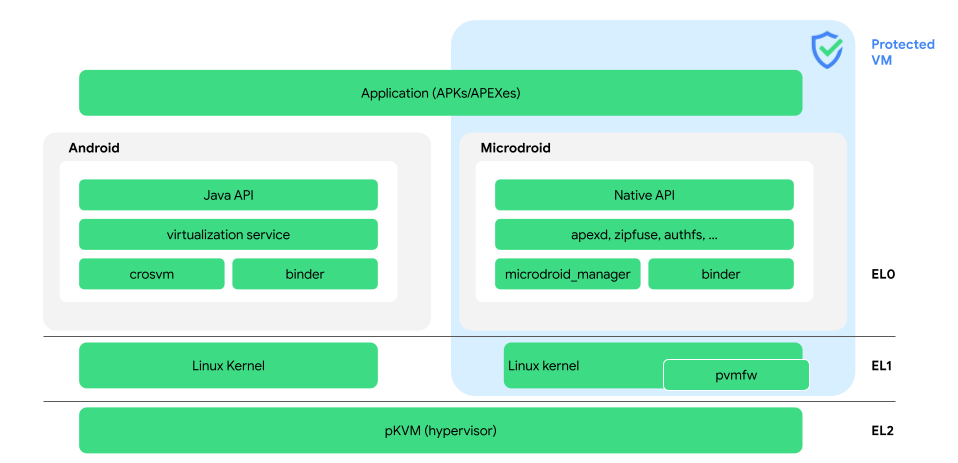
圖 1. AVF 架構。
以下是圖 1 中最重要的詞彙定義:
- apexd 和 zipfuse
- 安全掛接從主機匯入的 APEX 和 APK。
- authfs
- 透過 FUSE 檔案系統,在 Android 和 pVM (主機和訪客) 之間安全地共用多個檔案。
- 繫結器
- VM 間的主要通訊方式。
- crosvm
- 以 Rust 編寫的虛擬機器監視器。crosvm 會分配 VM 記憶體、建立虛擬 CPU 執行緒,並實作虛擬裝置的後端。
- 通用核心映像檔 (GKI)
- Google 認證的開機映像檔,內含從 Android Common Kernel (ACK) 來源樹狀結構建構的 GKI 核心,適合刷入 Android 裝置的開機磁碟分割區。詳情請參閱「核心總覽」。
- 管理程序
- AVF 使用的虛擬化技術,又稱為 pKVM。即使主機 Android 或任何其他 pVM 遭到入侵,管理程序仍可維護執行程式碼的完整性,以及 pVM 資產的機密性。
- Java API
- VirtualizationService Java API,僅適用於支援 AVF 的裝置。這些 API 為選用項目,不屬於
thebootclasspath。 - Microdroid
- Google 提供的迷你 Android OS,可在 pVM 中執行。
- Microdroid 管理員
- 管理 pVM 生命週期、pVM 內部和執行個體磁碟。
- 原生 API
- Android Native Developers Kit (NDK) 的子集。
- 受保護的以核心為基礎的虛擬機器 (pKVM)
- 請參閱「Hypervisor」。
- pVM 韌體 (
pvmfw) - 在 pVM 上執行的第一個程式碼會驗證酬載,並衍生每個 VM 的密碼。
pvmfw - 受保護的虛擬機器 (pVM)
與主要 Android 作業系統 (主機) 一併執行的互不信任隔離執行環境 (訪客)。pVM 安全性的重要層面之一是,即使主機遭到入侵,主機也無法存取 pVM 的記憶體。pKVM 是執行 pVM 的標準管理程序。
與現有的受信任執行環境 (TEE) 相比,pVM 提供更豐富的環境,包括執行名為 Microdroid 的迷你 Android 發行版本 (不過 Microdroid 也可以在未受保護的 VM 上執行)。pVM 可動態使用,並在受信任的環境中提供一組標準 API,適用於所有支援 pVM 的裝置。
- VirtualizationService
管理 pVM 生命週期的 Android 服務。
後續步驟
- 如要進一步瞭解為何需要 AVF,請參閱「為何需要 AVF?」。
- 如要瞭解如何使用 AVF 進行隔離編譯,請參閱「應用實例」。
- 如要深入瞭解 AVF 參考實作的架構,請參閱 AVF 架構。
- 如要瞭解 Microdroid,請參閱 Microdroid。
- 如要瞭解 AVF 如何處理安全性,請參閱「安全性」。
- 如要瞭解虛擬化服務的角色,請參閱 VirtualizationService。
- 如需 AVF 的原始碼或個別元件的深入說明,請參閱 AOSP 存放區

