您可以為搭載 Android 5.0 的新裝置啟用區塊式無線更新 (OTA)。OTA 是原始設備製造商 (OEM) 用於遠端更新裝置系統分區的機制:
- Android 5.0 以上版本會使用區塊 OTA 更新,確保每部裝置都使用相同的分區。區塊 OTA 會將整個分割區視為一個檔案,並計算單一二進位修補程式,確保產生的分割區確實包含所需位元,而非比較個別檔案和計算二進位修補程式。這樣一來,裝置系統映像檔就能透過 fastboot 或 OTA 達到相同狀態。
- Android 4.4 以下版本使用檔案 OTA 更新,可確保裝置包含類似的檔案內容、權限和模式,但允許中繼資料 (例如時間戳記和基礎儲存空間的版面配置) 根據更新方法在裝置之間有所不同。
由於區塊 OTA 可確保每部裝置都使用相同的分區,因此可使用 dm-verity 對系統分區進行加密簽署。如要進一步瞭解 dm-verity,請參閱「驗證開機程序」。
注意:您必須先擁有可用的區塊 OTA 系統,才能使用 dm-verity。
建議
如果裝置搭載 Android 5.0 以上版本,請在原廠 ROM 中封鎖 OTA 更新。如要為後續更新產生以區塊為基礎的 OTA,請將 --block 選項傳遞至 ota_from_target_files。
如果裝置搭載 Android 4.4 以下版本,請使用檔案 OTA 更新。雖然您可以透過傳送 Android 5.0 以上版本的完整區塊 OTA 來轉換裝置,但這需要傳送的完整 OTA 大小會比增量 OTA 大得多 (因此不建議使用)。
由於 dm-verity 需要啟動載入器支援,而這項支援僅適用於搭載 Android 5.0 以上版本的新裝置,因此無法為現有裝置啟用 dm-verity。
開發人員可訂閱 android-ota@googlegroups.com 的電子報,以便掌握 Android OTA 系統 (復原映像檔和產生 OTA 的指令碼) 的變更。
檔案與區塊 OTA
在檔案型 OTA 期間,Android 會嘗試在檔案系統層級 (逐一處理檔案) 變更系統分區的內容。更新作業不保證會以一致的順序寫入檔案、擁有一致的最後修改時間或超級區塊,甚至不會將區塊放在區塊裝置上的相同位置。因此,檔案型 OTA 在支援 dm-verity 的裝置上會失敗;在 OTA 嘗試後,裝置不會啟動。
在以區塊為基礎的 OTA 期間,Android 會為裝置提供兩個區塊映像檔 (而非兩組檔案) 之間的差異。更新會使用下列其中一種方法,在區塊層級 (位於檔案系統下方) 檢查裝置版本與對應的建構伺服器是否相符:
- 完整更新。複製完整系統映像檔很簡單,而且可以輕鬆產生修補程式,但也會產生大型映像檔,導致套用修補程式時的成本高昂。
- 增量更新。使用二進位差異工具可產生較小的映像檔,並簡化修補程式的套用程序,但產生修補程式本身時會大量使用記憶體。
注意: adb fastboot 會將與完整 OTA 相同的位元放置在裝置上,因此閃燈作業與區塊 OTA 相容。
更新未經修改的系統
對於搭載 Android 5.0 且系統分區未經修改的裝置,區塊 OTA 的下載和安裝程序與檔案 OTA 相同。不過,OTA 更新本身可能包含下列一或多項差異:
-
下載大小。
完整區塊 OTA 更新的大小與完整檔案 OTA 更新大致相同,而增量更新的大小可能只比前者大上幾 MB。
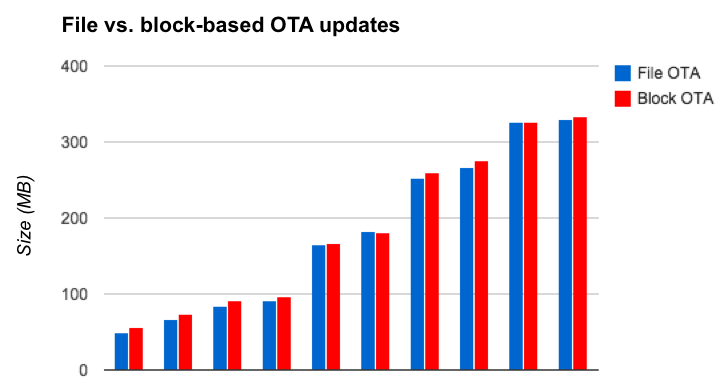
圖 1. 比較 Nexus 6 OTA 在 Android 5.0 和 Android 5.1 版本之間的大小 (不同目標版本變更)
一般來說,遞增區塊 OTA 更新的大小會大於遞增檔案 OTA 更新,原因如下:
- 資料保存。以區塊為基礎的 OTA 比以檔案為基礎的 OTA 保留更多資料 (檔案中繼資料、dm-verity 資料、ext4 版面配置等)。
- 運算演算法差異。在檔案 OTA 更新中,如果兩個版本的檔案路徑相同,OTA 套件就不會包含該檔案的資料。在區塊 OTA 更新中,要判斷檔案是否有少量或完全沒有變更,取決於來源和目標系統中修補程式運算演算法和檔案資料版面配置的品質。
- 對閃光燈和 RAM 故障的敏感度。如果檔案已損毀,只要檔案 OTA 未觸及損毀的檔案,就會成功;但如果系統分區偵測到任何損毀情形,則會導致區塊 OTA 失敗。
更新已修改的系統
如果裝置的系統分區已修改,且搭載 Android 5.0:
-
增量區塊 OTA 更新失敗。系統分區可能會在
adb remount期間或受到惡意軟體影響而遭到修改。檔案 OTA 可容許分區進行部分變更,例如新增非來源或目標版本的檔案。不過,區塊 OTA 不允許新增分割區,因此使用者必須安裝完整的 OTA (覆寫任何系統分割區修改內容),或刷新新的系統映像檔,以便日後啟用 OTA。 - 嘗試變更已修改的檔案會導致更新失敗。無論是檔案還是區塊 OTA 更新,如果 OTA 嘗試變更已修改的檔案,OTA 更新就會失敗。
- 嘗試存取已修改的檔案會產生錯誤 (僅限 dm-verity)。無論是檔案和封鎖 OTA 更新,如果啟用 dm-verity,且 OTA 嘗試存取系統檔案系統的修改部分,OTA 就會產生錯誤。
