Android 10 includes support for building
odm partitions using the Android build system.
About ODM partitions
Original design manufacturers (ODMs) customize system-on-chip (SoC) vendor board-support packages (BSPs) to their specific devices (their boards). This enables them to implement kernel modules for board-specific components, board-specific daemons, or their own features on hardware abstraction layers (HALs). They might also want to replace or customize SoC components.
In lower Android releases, such customizations prevented the use of a single
vendor image for devices with the same SoC (or with different SoCs, but in the
same family). In Android 10 and higher, you can use a
separate odm partition for customizations, which enables you to
use a single vendor image for multiple hardware SKUs.
Use product and ODM partitions
Android 9 added support for building
product
partitions, enabling the use of a single system image for multiple software
SKUs supplied by different product.img images. While the
product partition is intended for software SKUs, the
odm partition is intended for hardware SKUs.
With dedicated product and ODM partitions, you can use the system
partition to host generic code for sharing among many software SKUs, and the
vendor partition to host SoC-specific BSP code to share among
multiple devices based on the given SoC.
Using separate partitions has disadvantages, such as the difficulty in managing disk space (for example, you must reserve a limited amount of space for future growth). However, Android 10 support for dynamic partitions removes the disk issue, and makes repartitioning a device during an over-the-air (OTA) update possible.
ODM components
The odm partition contains the following ODM-specific components
(similar to the vendor partition), listed in the following table.
| ODM-specific component | Location |
|---|---|
| Loadable kernel modules (LKMs) | /odm/lib/modules/*.ko |
| Native libraries | /odm/lib[64] |
| HALs | /odm/lib[64]/hw |
| SEPolicy | /odm/etc/selinux |
| VINTF object data | /odm/etc/vintf |
init.rc
files |
/odm/etc/init |
| System properties | /odm/build.prop |
| Runtime resource overlays (RROs) | /odm/overlay/*.apk |
| Apps | /odm/app/*.apk |
| Priv-apps | /odm/priv-app/*.apk |
| Java libraries | /odm/framework/*.jar |
| Android Framework system configs | /odm/etc/sysconfig/* and /odm/etc/permissions/* |
No custom images
Don't use custom images because they lack support for the following:
- Installation of a module to a specific target. Custom images support copying artifacts into an image, but can't install a module into a specific partition by specifying the target partition as a part of a build rule.
- Soong.
custom_imagescan't be built using the Soong build system. - OTA update. Custom images are used as factory ROM images that can't be OTA-ed.
Maintain ABIs between partitions
The odm partition is an extension of the vendor
partition. When considering application binary interface (ABI) stability, keep
the following architecture in mind.
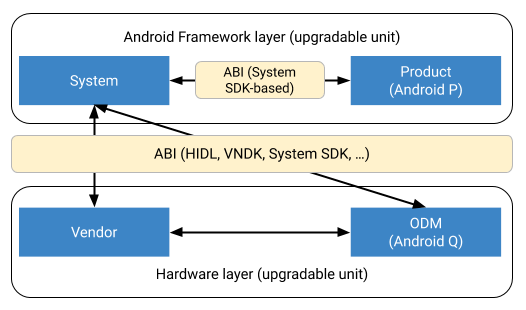
Figure 1. Maintaining ABI between partitions.
- There's no ABI stability between
odmandvendorpartitions. Both partitions must be upgraded at the same time. - The
odmandvendorpartitions can depend on each other, but thevendorpartition must work without anodmpartition. - The ABI between
odmandsystemis the same as the ABI betweenvendorandsystem.
Direct interaction between the product partition and the
vendor or odm partition isn't
allowed. (This is enforced by SEpolicy.)
Implement ODM partitions
Before implementing a new partition, review the related AOSP changes.
Set up ODM partitions
To set up odm partitions, include these build flags:
BOARD_ODMIMAGE_PARTITION_SIZEfor a fixed partition sizePRODUCT_USE_DYNAMIC_PARTITIONSandBOARD_ODMIMAGE_PARTITION_RESERVED_SIZEfor a dynamic partition sizeBOARD_ODMIMAGE_FILE_SYSTEM_TYPEfile system type used for the ODM imagePRODUCT_ODM_PROPERTIESfor/odm/build.propfor use within a$(call inherit-product path/to/device.mk), as inPRODUCT_ODM_PROPERTIES += product.abc=ok
Install a module to an ODM partition
Use these build flags to install a module to an odm partition:
device_specific: trueinAndroid.bpLOCAL_ODM_MODULE := trueinAndroid.mk
Enable Verified Boot
To prevent malicious software from tampering with odm partitions,
enable Android Verified Boot
(AVB) for those partitions (just as you do for vendor and
system partitions).
To enable AVB, include the build flag
BOARD_AVB_ODM_ADD_HASHTREE_FOOTER_ARGS. For details on configuring
AVB on dynamic partitions, see
AVB configuration
changes.
Treat /odm as another /vendor partition
To ensure that the system handles the odm partition as a
vendor partition, replace any hard-coded vendor
references with a set of hardware-oriented partitions (currently
odm and vendor). Notable vendor
reference locations in the platform include
dynamic
linker,
package
manager, and shell/libc.
