In Android 6 and higher, Wi-Fi service providers and packet analyzers have been restricted from retrieving a device's factory MAC address through the Wi-Fi stack from network requests. Starting in Android 10, additional restrictions are in place that limit access to device identifiers (IDs) to apps with the privilegedpermission level. This protects device IDs such as
- telephony IMEI, MEID, ESN, and IMSI numbers.
- build, SIM, or USB serial numbers.
Who can access device IDs
Device IDs are restricted on all Android 10 devices, even if apps target Android 9 or lower. Device IDs can be accessed by:
- The default SMS app.
- Apps with both
READ_PRIVILEGED_PHONE_STATEpermission in theManifest.permissionclass, and allowlisting in theprivapp-permission.xmlfile. These must also be loaded in thepriv-appdirectory. - Apps with carrier privileges as defined in UICC Carrier Privileges.
- A device owner or profile owner with
READ_PHONE_STATEpermission granted in theManifest.permissionclass. (Allowlisting isn't required.)
Privileged packages access
A package must be privileged to access device IDs. It must have
READ_PRIVILEGED_PHONE_STATE permission in the
Manifest.permission class, and be allowlisted in the
privapp-permission.xml file. For information on the allowlist
process, see Privileged
Permission Allowlisting.
For information on getting a unique ID for a nonprivileged package, refer to Common use cases and the appropriate identifier to use.
Restricted device IDs and randomized MAC addresses
To further restrict device IDs, all devices on Android 10 transmit randomized MAC addresses by default for both
probe and associated requests, and must have a different randomized MAC address
for each SSID. Don't use the device factory MAC address in client mode, soft
access point (AP), or Wi-Fi Direct use cases. It must remain hidden from
publicly accessible APIs that aren't privileged apps. Privileged apps that
require the factory MAC address to be returned are required to have
LOCAL_MAC_ADDRESS permission.
Users have the option to keep the default randomized MAC address that's assigned to each SSID. The option is viewable under Privacy in Settings > Network details. To learn about obtaining a randomized MAC address see Randomized MAC addresses.
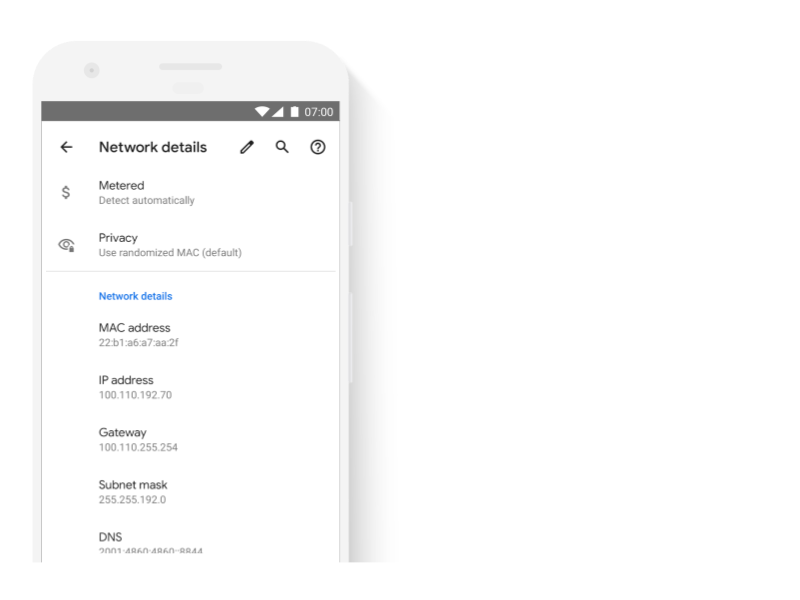
Figure 1.MAC address shows as randomized under Privacy in Network details.
Apps that invoke device ID APIs
Apps that invoke device ID APIs must meet the Android 10 requirements. Otherwise, when they try to access device IDs the following is returned:
- Apps targeting Android 10
SecurityExceptionis thrown from the device ID APIs.- Apps targeting Android 9 or earlier
- If they have the
READ_PHONE_STATEpermission, either anullresponse or placeholder data is returned. - If they don't, the device ID APIs throw
SecurityExceptionthat contains the name of the method called, and an indication that the calling app doesn't meet the requirements to access the requested ID.
For more on immutable device IDs see Nonresettable device identifiers and best practices for unique identifiers.
Testing
Apps must be prevented from accessing the device serial number and, where applicable, IMEI or MEID, SIM serial number, and subscriber ID. Apps with permission to access these IDs must also meet one of the criteria listed under Who can access device IDs.
