สิทธิ์ของ Android มีการควบคุมที่ช่วยเพิ่มการรับรู้ของผู้ใช้และจำกัด
การเข้าถึงข้อมูลที่ละเอียดอ่อนของแอป การกำหนดค่าสิทธิ์ใน Android 8.0 และเวอร์ชันที่ต่ำกว่ารวมถึงการอนุญาตพิเศษ ซึ่งหากไม่มีการอนุญาตพิเศษ แอปที่มีสิทธิ์จะถูกปิดใช้ แม้ว่าจะอยู่ในเส้นทาง priv-app ก็ตาม ใน Android 9 ขึ้นไป อุปกรณ์
ที่พยายามใช้แอปที่ไม่ได้อยู่ในรายการที่อนุญาตอย่างถูกต้องจะไม่บูต
Android 10 ได้เปิดตัวแนวคิดเกี่ยวกับบทบาท ซึ่งเป็นชื่อที่ไม่ซ้ำกันภายในระบบที่เชื่อมโยงกับข้อกำหนดและสิทธิ์บางอย่าง มอบหมายบทบาทให้กับแอปเพื่อให้สิทธิ์สำหรับ วัตถุประสงค์ที่เฉพาะเจาะจง และกำหนดค่าบทบาทเริ่มต้นโดยใช้ทรัพยากรการกำหนดค่าแพลตฟอร์ม
การปกป้องที่เพิ่มขึ้นเพื่อป้องกันแอปที่อาจเป็นอันตราย (PHA) ช่วยปรับปรุงสิ่งต่อไปนี้
- ความโปร่งใสเกี่ยวกับลักษณะการทำงานของแอปที่อาจเป็นอันตราย
- ผู้ใช้ควบคุมลักษณะการทำงานของแอป
- ดุลยพินิจของนักพัฒนาแอปเมื่อใช้ข้อมูลส่วนตัวที่ได้รับการคุ้มครองโดย สิทธิ์
การติดตั้งแพ็กเกจและสิทธิ์
ใน Android 9 และเวอร์ชันที่ต่ำกว่า ฟังก์ชันการติดตั้งแพ็กเกจและการควบคุมสิทธิ์
จะอยู่ในแพ็กเกจ PackageInstaller
(//packages/apps/PackageInstaller) ใน Android 10 ขึ้นไป ฟังก์ชันการควบคุมสิทธิ์
จะอยู่ในแพ็กเกจแยกต่างหาก PermissionController
(//packages/apps/PermissionController) รูปที่ 1
แสดงตำแหน่งของแพ็กเกจทั้ง 2 รายการใน Android 10
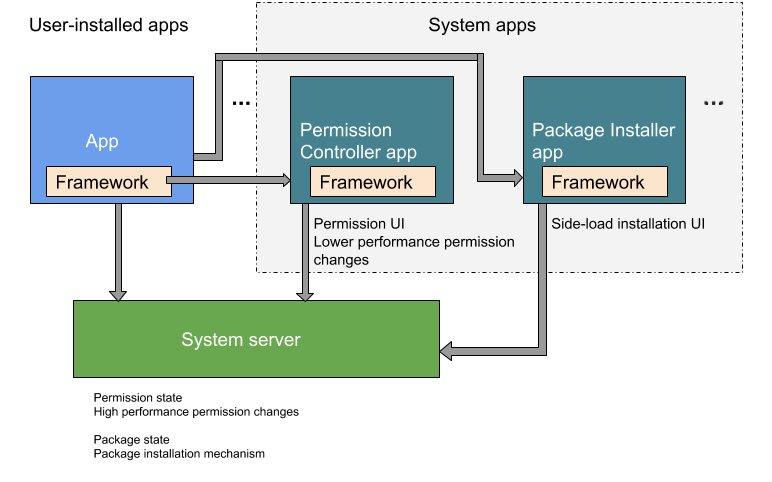
รูปที่ 1 ฟังก์ชันการติดตั้งแพ็กเกจและการควบคุมสิทธิ์ใน Android 10
รายการที่อนุญาตและการเข้าถึง
ใน Android 6.0 ขึ้นไป แอปจะขอสิทธิ์เข้าถึงสิทธิ์ที่เป็นอันตรายที่รันไทม์ Android 10 เพิ่มสิทธิ์รันไทม์การจดจำกิจกรรม (AR) ซึ่งจะแจ้งให้ผู้ใช้แก้ไขหรืออนุญาตสิทธิ์ที่เป็นอันตราย
Android 8.0 กำหนดให้คุณต้องเพิ่มแอปที่มีสิทธิ์ลงในรายการที่อนุญาตอย่างชัดเจนใน
ไฟล์ XML การกำหนดค่าระบบในไดเรกทอรี /etc/permissions
ใน Android 9 ขึ้นไป สิทธิ์ที่มีสิทธิ์พิเศษต้องอยู่ใน
รายการที่อนุญาต
หรืออุปกรณ์จะบูตไม่ได้
Android 7.0 ได้เปิดตัวเนมสเปซ สำหรับไลบรารีแบบเนทีฟเพื่อจำกัดการเข้าถึง API ภายในและป้องกันไม่ให้แอปเข้าถึงไลบรารีแพลตฟอร์มโดยไม่ตั้งใจ ซึ่งจะแยกไลบรารีของระบบออกจากไลบรารีของแอป และผู้ผลิตอุปกรณ์สามารถเพิ่มไลบรารีเนทีฟของตนเองได้
ตั้งแต่ Android 10 เป็นต้นไป แอปต้องมีทั้ง สิทธิ์ลายเซ็นและความยินยอมของผู้ใช้เพื่อ เข้าถึงเนื้อหาบนหน้าจอของอุปกรณ์ แอปที่มีสิทธิ์ซึ่งอาศัยฟังก์ชันการจับภาพแบบเงียบ เช่น การถ่ายภาพหน้าจอ ควรใช้คลาส MediaProjection แทน
Android 15 กำหนดให้คุณต้องเพิ่มในรายการที่อนุญาตอย่างชัดเจน
สำหรับสิทธิ์ลายเซ็นของแพลตฟอร์มที่แอปที่ไม่ใช่ระบบขอ หรือที่ขอใหม่โดยการอัปเดต
แอปของระบบในไฟล์ XML การกำหนดค่าระบบในไดเรกทอรี /etc/permissions
ความโปร่งใสและความเป็นส่วนตัว
ใน Android 6.0 ขึ้นไป ระบบจะป้องกันที่อยู่ MAC ของโรงงานของอุปกรณ์จากการเข้าถึงโดยผู้ให้บริการ Wi-Fi และเครื่องมือวิเคราะห์แพ็กเก็ต ข้อจำกัดเพิ่มเติมใน Android 10 จำกัดไม่ให้แอปเข้าถึงตัวระบุ (รหัส) ของอุปกรณ์ที่เปลี่ยนแปลงไม่ได้ เว้นแต่จะ อยู่ในรายการที่อนุญาตสำหรับสิทธิ์ที่มีสิทธิ์ (ส่วน การเชื่อมต่อมีการอภิปรายที่เกี่ยวข้องเกี่ยวกับ ตัวระบุ อุปกรณ์ เนื่องจากส่วนนี้ส่งผลต่อผู้ให้บริการ)
ใน Android 9 และต่ำกว่า ผู้ใช้จะเลือกแบบถาวรเมื่อให้สิทธิ์เข้าถึงตำแหน่งแก่แอป ตั้งแต่ Android 10 เป็นต้นไป ฟีเจอร์สิทธิ์เข้าถึงตำแหน่งแบบ 3 สถานะจะให้ตัวเลือกแก่ผู้ใช้ 3 ตัวเลือกในการอนุญาตให้แอปเข้าถึง ตำแหน่งของอุปกรณ์ ข้อกำหนดด้านสิทธิ์เหล่านี้มีผลกับแอปใน Android 10 ไม่ว่า SDK เป้าหมายจะเป็นอะไรก็ตาม
กำหนดค่าสิทธิ์สำหรับฟีเจอร์ความโปร่งใสและความเป็นส่วนตัวอื่นๆ ตั้งแต่ Android 10 เป็นต้นไป
- การช่วยเตือน
การเข้าถึงตำแหน่งในเบื้องหลังจะแสดงต่อผู้ใช้เมื่อแอปเข้าถึง
ตำแหน่งของอุปกรณ์โดยใช้
ACCESS_FINE_LOCATIONสิทธิ์ในเบื้องหลัง - ข้อมูลที่เกี่ยวข้องกับความสัมพันธ์ของรายชื่อติดต่อซึ่งจัดการโดยคอมโพเนนต์ผู้ให้บริการรายชื่อติดต่อ จะได้รับการเข้าถึงในลักษณะที่แตกต่างกัน กล่าวคือ แอปจะเขียนหรืออ่านข้อมูลความสัมพันธ์ของรายชื่อติดต่อในฐานข้อมูลไม่ได้ ซึ่งจะส่งผลต่อ API ที่เกี่ยวข้องกับผู้โทร
การกำหนดค่าที่มีประสิทธิภาพยิ่งขึ้น
เราได้ปรับปรุงการกำหนดค่าสิทธิ์สำหรับ Android 6.0 ขึ้นไป
- ความสามารถโดยรอบสำหรับบริการที่เปิดตัวโดย
initจะเก็บทุกด้าน ของการกำหนดค่าบริการไว้ในไฟล์.rcเดียว เมื่อตั้งค่า ความสามารถสำหรับบริการที่ไม่ได้เปิดตัวโดยinitให้กำหนดค่าความสามารถของระบบไฟล์โดยใช้fs_config.cแทน - Android 7.x และต่ำกว่าจะขยายกลไกของรหัส Android (AID) โดยใช้
android_filesystem_config.hไฟล์เฉพาะอุปกรณ์เพื่อระบุความสามารถของระบบไฟล์และ/หรือ AID ที่กำหนดเองของผู้ผลิตอุปกรณ์ Android 8.0 ขึ้นไปรองรับวิธีการใหม่ ในการขยายความสามารถของระบบไฟล์ - ใน Android 8.0 การจัดการคำสั่ง USB จะย้ายออกจากสคริปต์เฉพาะอุปกรณ์
init(การแทนที่เลเยอร์ HAL) และไปอยู่ใน daemon USB ดั้งเดิม ต้องติดตั้งใช้งานอินเทอร์เฟซ USB HAL ในอุปกรณ์ทุกเครื่องที่เปิดตัวใน Android 8.0 ขึ้นไป
